Now that increasingly more people are using cryptocurrencies for mainstream transactions, given that was the original concept behind the creation of such digital assets in the first place, the need to familiarize themselves with using private keys has a much greater importance. This involves understanding what they are, how they function, plus how to keep them safe and secure.
But what is a private key? Essentially, private keys are secret cryptographic keys comprised of unique alphanumeric codes, which are basically passwords or digital signatures. This allows the owner of a private key to sign transactions and control access to their cryptocurrency and/or digital assets, providing the most secure way to verify authenticity and ownership.
Whenever users wish to utilize cryptocurrencies for transactions, private key cryptography is deployed to generate a corresponding public key. This process is commonly known as public key derivation, while the public key can then be shared freely with others to send and receive funds, without exposing your private key at any time.
Essentially, there are two main types of cryptocurrency wallets, usually referred to as “custodial” and “non-custodial” wallets.
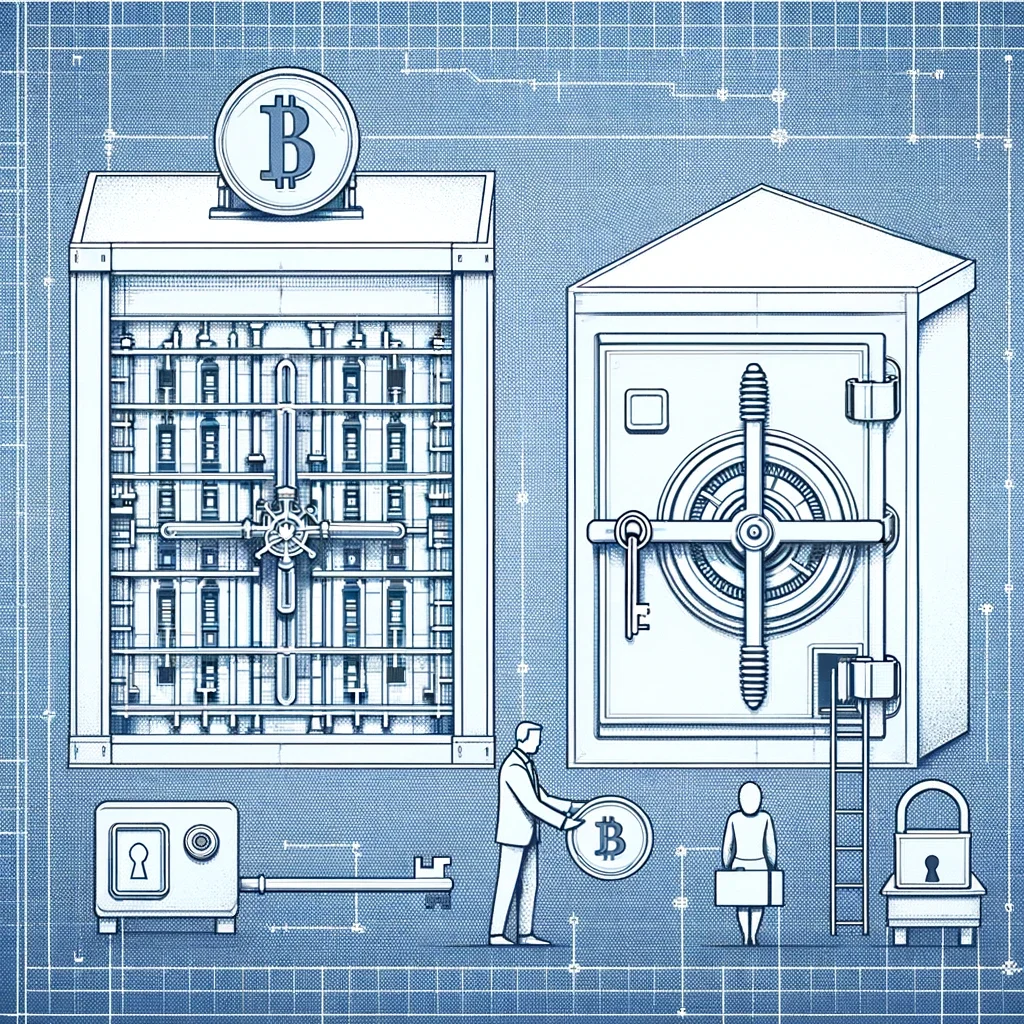
Custodial wallets are a third-party service that allows users to store cryptocurrencies, much like depositing money in a bank. This enables users to bypass the storage of private keys, given that exchanges or payment gateways will store the keys for you. By comparison, non-custodial wallets involve hardware devices whereby you store the keys yourself.
Both custodial and non-custodial wallets can also be referenced additionally. So-called “hot wallets” are those connected to the internet, while “cold wallets” are without any connection. The latter is typically the most common application for non-custodial wallet usage.
When considering the storage and security of cryptocurrency holdings, people often ask the following question: Should you trust custodial wallets?
In the realm of custodial wallets, many exchanges, for example, commonly provide custodial wallet services. Whenever users purchase cryptocurrencies, these digital assets will usually be deposited in a custodial wallet, which essentially means the exchange is acting as your custodian, holding your private keys and safeguarding the security of your funds.
Many prestigious cryptocurrency trading platforms, such as Binance, and cryptocurrency payment gateways like UniPayment, are actively taking measures to provide users with more stringent layers of security protection.
Some of the biggest crypto exchanges tend to provide an additional layer of security, holding their customer funds offline using non-custodial hardware cold wallets, and we’ll explain more about those later in this article. Although online custodial hot wallets can sometimes be considered less secure, convenience and ease of use make them popular, along with the backup of handing responsibility to the exchange.
Should anyone lose their non-custodial wallet passwords, it can potentially lead to the loss of their crypto assets. But if you were to forget your crypto exchange password, reputable exchanges will have a recovery and reset process to acquire new passwords, therefore it’s always recommended to follow all their security recommendations.
A special case is the external wallet service provided by UniPayment. It not only supports users in transacting with non-custodial wallets but also returns the control of private keys back to the users. Although the challenge of protecting private keys still exists, this approach undoubtedly introduces a higher level of security for payment gateways.
Private keys form an integral part of B2B (Business-to-Business) cryptocurrency gateway usage, being part of the digital handshake during the process of transactions that confirm authentication. For most of us, the role of private keys is part of our daily activity involving digital assets, meaning that we can often take for granted the encryption and data security they provide.
When conducting transactions via crypto payment gateways, private keys play several critically important roles:
UniPayment offers developer-friendly integration options that are ideal for a wide range of projects, irrespective of their scale and nature. The API and plugins are suitable for all the virtual stores and eCommerce platforms, whether it is a basic or enterprise-level integration.
“Keep it secret. Keep it safe.” – The famous words of Gandalf the wizard in Lord of the Rings, upon giving Frodo Baggins the One True Ring in a sealed envelope. It’s an amusing comparison to use when thinking about keeping your private keys confidential and secure, given they equate to complete ownership and control of your digital assets.

Think of that envelope as being akin to our digital wallets, with the ring as our private key. To store private keys securely, we don’t want anyone else to know their contents or have access. Keeping your private keys confidential and secure is essential, given they are irrecoverable if lost or stolen. Understanding how to store private keys these days is critical knowledge, making proper storage and protection of private keys a priority for anyone who owns digital assets.
While there are different kinds of blockchain wallets available, depending on the kinds of hardware devices or software platforms you’re using, basic advice for storing blockchain wallet private keys is based on common sense. These are some tips to consider as best practices for storing private keys, via our partners at Chainstack:
Remember, these are simple and common-sense ways to protect your private keys. They’re also useful to consider if you need to recover information, such as a lost private key. This is why it’s just as important to store your Trust Wallet private key or Bitcoin private key in a safe, offline location. And this brings us to look at some advanced security measures, providing increased safety for our digital assets, and contingency plans we should also keep in mind.
When it comes to safe usage and protection of our private keys, for the majority of people, using the commonsense tips we’ve already highlighted is often enough. Nevertheless, adequate management of these keys can be taken to a whole other level, and experienced cryptocurrency users can also utilize advanced key storage security techniques.
These can include utilizing hardware wallets for added security. Instead of relying upon software, some individuals and organizations use dedicated offline devices to store their private keys, featuring hardware keys (FIDO2) or trusted platform modules (TPMs). The main security benefit is the utilization of enhanced encryption, therefore significantly reducing the risks of unauthorized access.
Hardware security modules (HSMs) tend to be deployed by larger enterprises, typically when controlling much bigger volumes of digital assets and cryptocurrencies. Somewhat like the cryptocurrency version of a bank vault, they offer the most secure solution for key storage, alongside managing a wide variety of cryptographic operations.
But regardless of how safe and secure your digital assets may seem, we should always have some backup options as part of our key management strategy, enabling full recovery of private keys. Consider formulating a recovery plan and storing it in a safe location, either as an encrypted digital document or in physical document form, only shared with trusted individuals.
Ensure these individuals fully understand how to access and manage your digital assets, along with any safety and security protocols you have in place. Should you ever become incapacitated or unable to manage your cryptocurrency holdings, your trusted individuals can then act on your behalf and will have the relevant authority to do so. Always remember to review this contingency plan regularly, and keep trusted individuals informed.